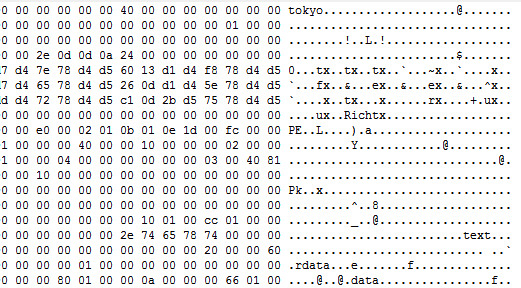
During Christmas holidays, Lab52 has been analyzing a sample which loads an artifact that we have decided to refer to as “TokyoX” since no similarities have been found as to any known malware, which we usually detect in open sources. However, we cannot confirm so far that it is indeed a new family of malware. […]
Cuba Ransomware Analysis
Due to the recent warning published by the FBI about Cuba ransomware (original FBI warning no longer available online for unknown reasons), from Lab52 we decided to publish some information about this ransomware family. Despite the fact that the ransomware has been named Cuba, there is no clear evidence linking the country to the implementation […]
Winter Vivern – all Summer
In July, 2021, Lab52 found a currently active infection campaign (domain still up at the time of this writing) attributed to a group referred as Wintervivern after a report published by the research team from DomainTools. As the starting point for this research, we recently noticed that unless properly obfuscated, some functions in XLM macro […]
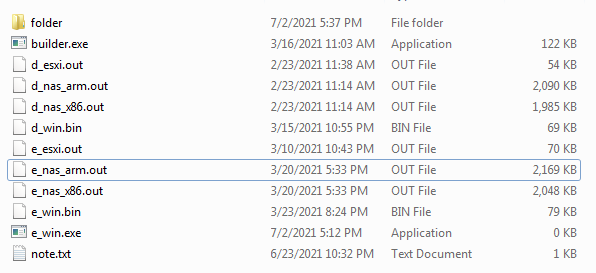
Quick review of Babuk ransomware builder
Last week, the builder for the Babuk ransomware family was leaked online. Lab52 has obtained and analyzed this builder sample determining that it is very likely to be authentic. After their recent official move from Ransomware as a Service to data leaks extortions, someone uploaded to virusTotal the ransomware builder for unknown reasons, and it […]
Literature lover targeting Colombia with LimeRAT
In the middle of the current brouhaha in Colombia, besides the intense hacktivism activity, some actors might be trying to take their move. Several campaigns aimed to Colombia have been detected, but today we will talk about one with a couple interesting details in their kill chain. This actor is starting the infection via email […]
Updates on OwlProxy malware
During the analysis of some malicious artifacts collected from an incident, we have recently detected a sample that has caught our attention, the sample was deployed on a server exposed to the Internet and was packed with “VMProtect”. After analyzing this malware sample we could see that it was a recent version of a tool […]