During our analysis of the Penquin-related infrastructure we reported in our previous post, we paid special attention to the malicious binaries contacting these IP addresses, since as we showed in the analysis, they had been used as C2 of other threats used by Turla. One threat that makes contact with the 82.146.35[.]240 address in particular […]
Another cyber espionage campaign in the Russia-Ukrainian ongoing cyber attacks
From lab52, in connection to the latest events related to the Russia’s ongoing cyberattacks in Ukraine, beyond destructive artifacts seen like Wipers and others, a new wave of malicious office documents (hereinafter maldocs) has been observed attempting to compromise systems leveraging a variant of well-know and open-source malware known as Quasar RAT. Recently, we identified […]
Very very lazy Lazyscripter’s scripts: double compromise in a single obfuscation
In July of 2021, we identified an infection campaign targeting important European entities. During this investigation we could identify the threat actor behind these attacks as LazyScripter, an emerging APT group pointed by MalwareBytes in February 2021. Through our analysis, we could track their activity with precise dates in 2021 based on their samples. Furthermore, […]
Looking for Penquins in the Wild
During 2020 Leonardo analysts discovered and published a very in depth analysis of a threat known as Penquin, attributed to the APT group Turla. 32-bit samples of this threat had been detected and analyzed by Kaspersky before, but the analysis in this most recent publication was focused on a new 64-bit sample. It firstly caught […]
New TransparenTribe Operation: Targeting India with weaponized COVID-19 lure documents
Over the last months, lab52 has been researching an attack campaign which targets government and military personnel of India. In fact, targeting the Indian government seems to be one of the key indicators of the group that may be behind this attack. Furthermore, some of the artifacts and infrastructure used to carry out the novel […]
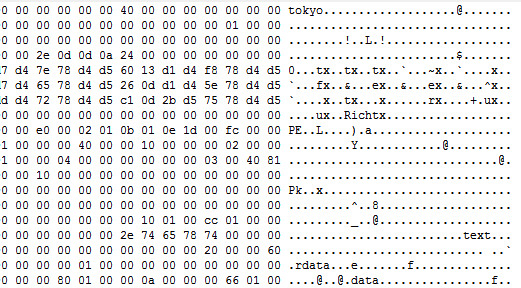
TokyoX: DLL side-loading an unknown artifact (Part 2)
As we mentioned in the previous post, we have performed an analysis of the threat which, lacking further information, we have not been able to identify it as a known threat. Thus, for the moment, we will keep referring to it as TokyoX. This threat can only be found in memory, since it is encrypted […]