S2Grupo’s Threat Hunting team has carried out an investigation on the occasion of the NATO summit held in Madrid on June 29th and 30th on possible APT group campaigns that could have targeted this event.
In this line, we have investigated those domains that had as part of the name any of the keywords provided by the Lab52 cyberintelligence team. In addition, they have been contextualized through WHOIS information.
The graph below represents the time distribution of domain name creation and the keywords used in their name. The 15 most used keywords are shown. The time frame represented goes frome April 1st toJune 22nd.

The first thing to note is the shape of the graph. The lower peaks correspond to Saturdays and Sundays of each week. The most logical explanation for this phenomenon is simply that fewer domains are registered on weekends.
Keyword nato
The second most used keyword in the SLD of the domains detected between April 1st and June 22nd is nato. In the graph below two peaks of domain registration can be observed. These peaks correspond to the dates April 11th and April 25th.
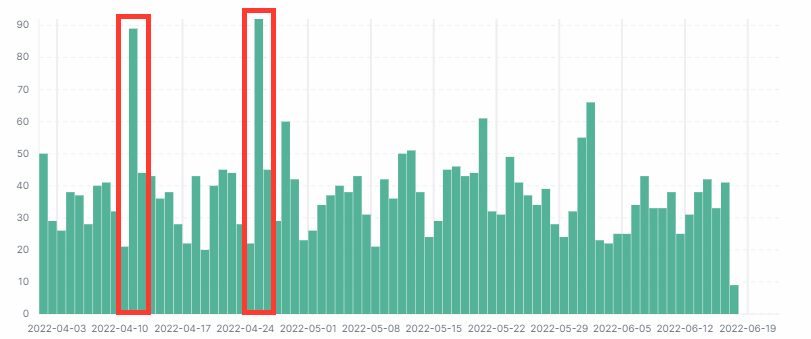
When investigating these results, the following is found, none of the 42 domains registered on April 11th containing nato in their SLD seem to be related to the North Atlantic Treaty Organization.
| chinatownone[.]com | didonatoroberto[.]com |
| doctoranatomy[.]com | donatoelectroshop[.]com |
| etnatoys[.]com | fascinators[.]info |
| genatonerscanner[.]com | guidedanatomy[.]com |
| hnsartesanato[.]com | homecareexterminators[.]com |
As for the peak on April 25th, several patterns have been observed in the registered domains:
- Domains with the word anatomy:
There are 22 domains containing the word anatomy. They were registered by the same company, Ascio Technologies, Inc. Danmark and all of them registered in Norway. In addition, the word leader seems to be recurrent among these domain names.

- Domains registered by NameCheap, Inc:
A large part of the domains registered on May 25th that have nato in their SLD were registered by NameCheap, Inc.

A closer look at these domains shows that they were registered in the United States and Iceland.
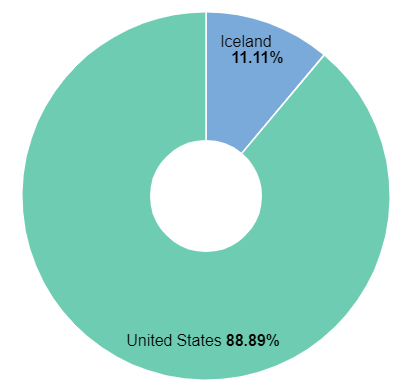
The domains registered in Iceland do not appear to be related or follow a pattern.
| ajinatoto[.]online |
| anatomyofguitartone[.]marketing |
| cltvedbugexterminator[.]com |
| thetubinator[.]com |
However, those that were registered in the United States do appear to be related to each other. Moreover, they all seem to refer to the North Atlantic Treaty Organization. In a way, it seems that these domains are intended to masquerade as legitimate domains of the organization. All the domains are shown below.
| actnato[.]com | brandnato[.]com | econato[.]com | fnato[.]com |
| freenato[.]com | gamenato[.]com | historynato[.]com | insidenato[.]com |
| natobank[.]com | natoblog[.]com | natoconference[.]com | natodesign[.]com |
| natoexpo[.]com | natofinance[.]com | natofurniture[.]com | natogames[.]com |
| natohealth[.]com | natointelligence[.]com | natomap[.]com | natomarket[.]com |
| natopartner[.]com | natophone[.]com | natopost[.]com | natopress[.]com |
| natoq[.]com | natosecret[.]com | natosport[.]com | natostaff[.]com |
| natotoday[.]com | natotravel[.]com | natoworks[.]com | netnato[.]com |
To avoid results for words containing the letters nato as in the previous case of domains with the word anatomy, another approach was to search for domains starting with the word nato. Those domains registered by NameCheap, Inc. have been excluded because they have been collected in the previous analysis. The graph shows a peak registration on June 6th.
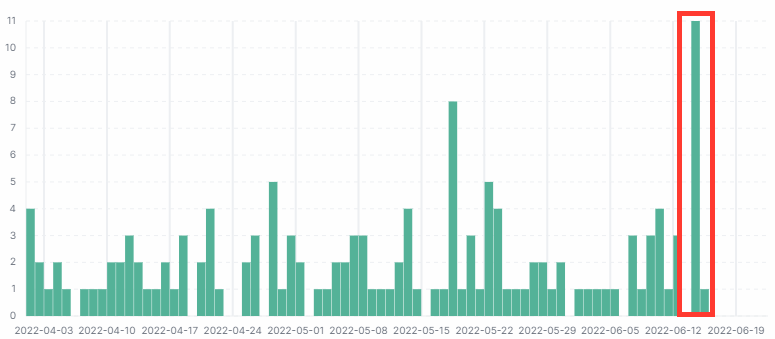
Most of these domains were registered by PublicDomainRegistry in Poland. Both the SLD and TLD of these domains are suspicious and appear to be malicious.
| natofrontline[.]com | natofrontline[.]info |
| natofrontline[.]net | natofrontline[.]online |
| natofrontline[.]site | natofrontline[.]store |
| natofrontline[.]tech | website |
Keyword otan
After analysing the domains containing the keyword otan, any relation to NATO has been ruled out. Only two domains have been found that could be related: otan[.]info and fuckotan[.]com.
Keyword summit
The graph below represents the time distribution of domain registration with the word summit in the SLD. Several peaks of domain registration can be seen.

Most of the domains in the three peaks were registered by GoDaddy.com (55.72%) and in the United States (68.47%).

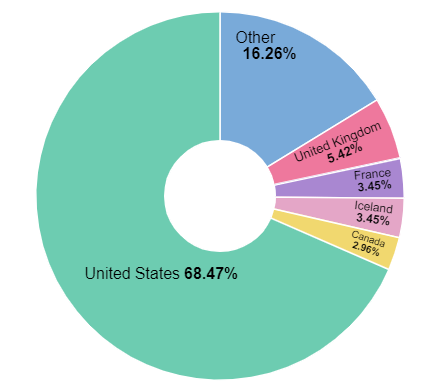
Analysis of these domains has led to the conclusion that they are likely to be used for fraudulent activities. The SLDs were probably designed to get the victim’s attention and get them to access the domain. Here are some examples.
| newworldleadershipsummit[.]com | theworkplacesummit[.]com |
| blockchain-one-to-one-summits[.]com | audisummitforprogress[.]com |
| beautyrichsummit[.]com | biotech-summit[.]com |
| chemical-recycling-summit[.]com | globalmanufacturingsummit[.]org |
| munich-newspace-summit[.]org | womensinclusionsummit[.]org |
Therefore, this research leads us to conclude that most of the domains identified as suspicious during the analysis will be used for malicious purposes, either as part of a Command and Control infrastructure or through disinformation campaigns. There is no doubt that the NATO summit held in Madrid during the last week of June has been used as a medium for cybercriminal purposes.



Leave a Reply