Lab52 offers a service which is completely focused on geopolitics and cybersecurity. Currently, there is an important correlation between geopolitics and cyberattacks. All the cyberattacks promoted by states have their origins or roots in the ancient framework of military espionage and intelligence ([1]). For that reason, Lab52 is permanently following and investigating the new updates related to global geopolitical affairs. In the meantime, we are researching the most recent IOC (Indicators of Compromise) used by threat groups in their campaigns.
Since ancient times of history, warfare has undergone a major evolution. The physical and the psychological attacks in warfare have been applied by the most powerful armies against their enemies. Moreover, for decades some offensive states have developed cyber resources and tools to be used as weapons in warfare ([1]). Currently, there is a significant relation between cyberattacks and the geopolitics plan executed by the most powerful nations to achieve their strategic goals in international relations and military conflicts.
In order to understand the evolution of this relation we should know that there are two type of military conflicts: symmetric and asymmetric, also known as conventional and unconventional battles ([2]). Symmetric conflicts are carried out by professional militarists and the asymmetric or unconventional battles are started by “guerrillas”, frequently and indirectly managed by states.
Cyberattacks promoted by states belong to hybrid strategies which are included in unconventional warfare. A hybrid war is a kind of conflict which rose after the Cold War and is defined as “a range of different modes of warfare including conventional capabilities, irregular tactics and formations, terrorist acts including indiscriminate violence and coercion and criminal disorder” ([3]). Through the years, this concept has been expanded and currently its definitions include offensive special cyber operations and psychological operations.
In the graph below there are several specializations that compose the hybrid warfare ([4]):
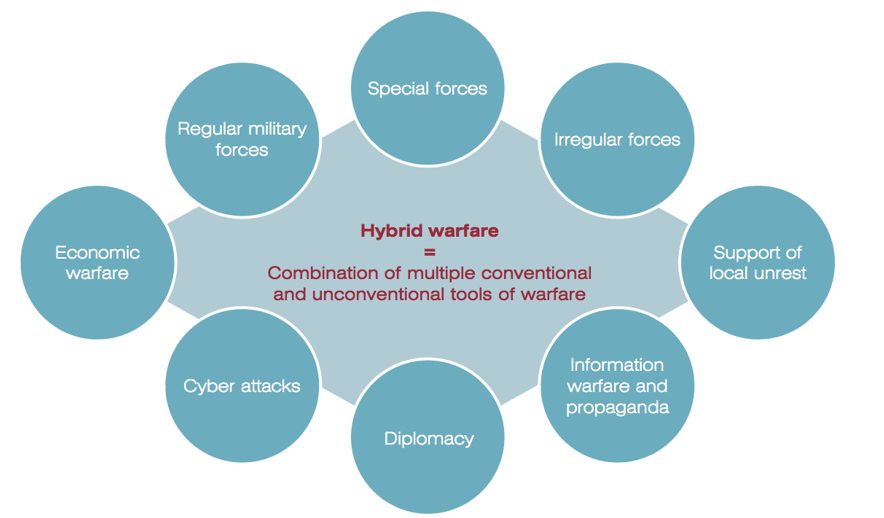
Illustration 1 Hybrid warfare Factors
As we can see in the graph, a hybrid war consists of multidisciplinary resources and tools. Among the different elements that make up hybrid warfare are cyberattacks. Nowadays, cyberattacks are one of the main military resources used in all the geopolitical conflicts around the world. There are several ranges of dangerousness and threat actors: individual hackers, criminal activities, espionage operations, and nation-state warfare ([5]). In the graph below shows the most important levels in a cyber threat spectrum:
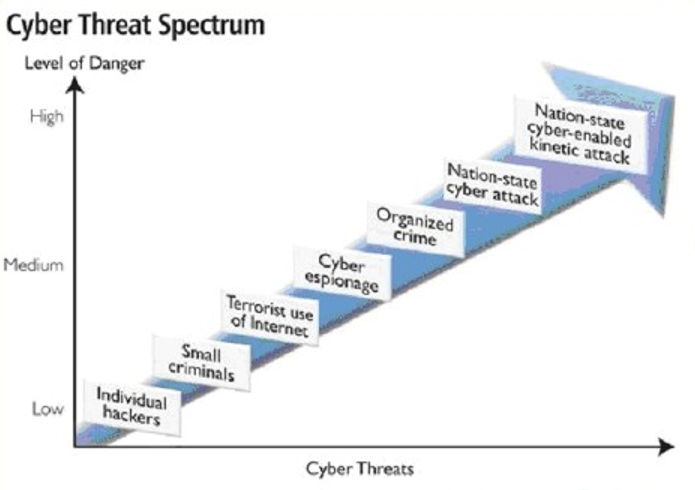
As seen in the spectrum graph the most threatening and dangerous stages are integrated by Nation-state. Usually, this kind of threat actor has a main goal: collecting classified information from other governments or from relevant organizations. Furthermore, the critical national infrastructures are an important target for all APT groups, in this case, the main target organizations would be from the energetic field, hospitals, airports or communication tools among others.
A paradigmatic international case that shows the importance of the relation between geopolitics and cyberattacks happened in 2014 with the Crimea Annexation by Kremlin. Ukraine suffered a major military operation of the hybrid war with cyberattacks that generated changes within the internal and external policies of the country. In 2015 three Ukrainian electrical companies were cyberattacked by BlackEnergy, a threat group supposedly associated to Russia. This threat actor managed to disable the control and non-control systems computer ([6]).
Geopolitically, the alleged cyberattack campaign executed by Russia in Ukraine is part of a geostrategic plan which is included in the Gerasimov method. Usually, cyberattack campaigns promoted by Nation-states belong to a geostrategic plan to manipulate and persuade the enemy society. Their main goal is to get a beneficial situation for the actor which is executing the operation ([7]).
The following graph shows the procedure and the steps of the Gerasimov method. This system has been used to carry out hybrid attacks where cyberattacks are a key step in the process:
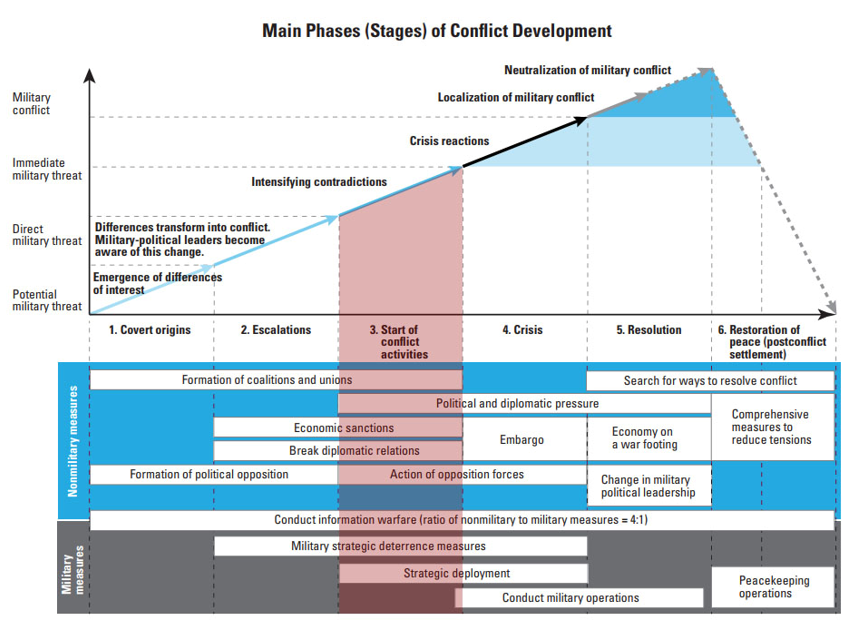
As seen in the table, cyberattacks to the governmental organizations and critical infrastructures are very effective in the third stage of the hybrid attack process ([8]):
Stages of Hybrid Warfare
| 1st Stage | Covert origin: The conflict begins some time before that the violence gets started. The threat actor, through a specific disinformative campaign applied to the specific society tries to influence the decision makers of a country and the public opinion. The main goal of this stage is to fragment the opinion of the society by means of a sensitive topic. | |
| 2nd Stage | Increase tension: Once tension and social fragmentation has increased within the victim country, the external actor will carry out a strategy of diplomatic isolation against its victim and apply economic sanctions. On the other hand, he will also carry out a disinformation dissemination campaign with the aim of generating social discontent in the victim country. | |
| 3rd Stage | Start hostile operations: In this stage the hostile actor could execute operations that are related to cyberattacks, military presence next to the borders, or hostile actions with clear violence among both parts of the fragmented society. In this phase, cyberattacks could be used to sabotage critical infrastructure organizations like grids, steal classified information to defame personalities from the government. The main goal of this stage is to increase the tension to higher rates to justify the external intervention from the threat actor who is applying the strategy. | |
| 4th Stage | Crisis: The threat actor does a military intervention claiming humanitarian help to the citizens. In the meantime, it promotes economic sanctions and continues carrying out the disinformation strategy in order to justify the military occupation. | |
| 5th Stage | Resolution: The threat actor will try to use all the governmental resources to disturb the peace in the country and begin working on his own interests. | |
| 6th Stage | Disturbance of the Peace: In the last stage, the hostile actor’s intervention will look to promote the local groups which support him. After that, he will begin a significant campaign to promote the supporters’ local group internationally looking for the International Community approbation. |
All the cyberattacks promoted by a Nation-state are aimed to support a geopolitical strategy. The cyber resources and tools from a State is becoming a fundamental military good for their offensive and defensive weapons. If a State or an important organization does not have a proper cyber defensive structure to keep their classified information secure, then it is highly vulnerable and weak for threat groups.
References:
[1] The Impact of Cyber Threat on Geopolitics: A Paradigm Shift in International Relations https://www.securityweek.com/understanding-geopolitics-key-analyzing-cyber-espionage-german-intelligence-service
[2] http://yris.yira.org/comments/2323
[3] THE MOUSE, THE TANK AND THE COMPETITIVE MARKET: A NEW VIEW OF HYBRID WAR Graham FAIRCLOUGH*
[5] Cyber Threats in Hybrid Warfare: Securing the Cyber Space for the RSAF by LTC Anthony Wong, MAJ Christopher Eng, CPT Ronald Loh Ming Yao & CPT Jeffrey Ng
[7] Colom Piella. (2018) ¿Guerra híbrida a la rusa? algunos apuntes sobre “la doctrina gerasimov” (THIBER REPORT Nº2). http://www.thiber.org/2018/04/06/thiber-report-no2-guerra-hibrida-a-la-rusa-algunos-apuntes-sobre-la-doctrina-gerasimov/
[8] UGR. (2018). La doctrina Gerasimov y el pensamiento estratégico contemporáneo. https://www.ugr.es/~gesi/Doctrina-Gerasimov.pdf




Leave a Reply