Although it is true that the terrestrial, maritime, air, space, and cyberspace domains are the usual focus of analysis, the radio frequency spectrum also reflects the current geopolitical tensions. Within it, states systematically employ capabilities related to influence, interference, and command and control.
LAB52 has SIGINT acquisition capabilities in the radio frequency spectrum, which have enabled it possible to identify behavioral patterns associated with certain actors, particularly in relation to FIMI (Foreign Information Manipulation and Interference) capabilities, affecting not only the cyberspace domain but also the radio frequency spectrum [1]. This article aims to present activity in the radio frequency spectrum throughout 2026 and its correlation with the state of international relations. For security reasons, any activity attributed to allied countries has been excluded from the analysis.
RELEVANT ACTIVITY IN 2026
The first months of 2026 have seen a convergence of escalations in the electromagnetic spectrum by certain actors which, when analyzed collectively, reveal a pattern consistent with doctrines of competition in the information domain. The following section summarizes the most analytically relevant events, detailed in Table 1.
| Date | Actor | Signal/Freq | Event |
| Ene 2026 | Russia | UVB-76 / 4.625 MHz | “Swan Lake” transmission |
| Feb 2026 | Russia | UVB-76 / 4.625 MHz | Encoded voice message: “NZHTI 70 45”. |
| Feb 2026 | Iran | V32 / 7.910 MHz | First transmission of the Persian numbers station V32. |
| Mar 2026 | Iran | Jammer / 7.910→7.842 | Adaptive jammer coincides with V32 frequency shift (+/- 68 kHz). |
| Mar 2026 | China | CNR1 / 9.849 MHz | Increased activity attributed by open sources to the Firedrake system. |
| Apr 2026 | North Korea | GPS spoofing | GNSS interference alerts reported by ICAO. Civil aviation routes Incheon–Tokyo affected. |
| Apr 2026 | Iran | IRIB / 1.449 MHz | IRIB broadcasts 33 consecutive transmissions with elevated power levels. |
| May 2026 | North Korea | NK Jammer / 6.249 MHz | Jammer detected attributed by open sources to North Korea |
Table 1 – Relevant radio spectrum activity observed in 2026
Data obtained by LAB52 has enabled the detection of several anomalies in radio communications throughout 2026.
First, on 28 February, a Persian-language numbers station was detected on the 7.910 kHz frequency, identified by the community as V32. This date coincides with increased tensions between Iran, the United States, and Israel. One possible attribution is its association with the Iranian opposition in exile. This is due to the fact that Iranian jamming activity adapted the frequency (from 7.910 kHz to 7.842 kHz) in order to block the signal, suggesting spectrum monitoring capability and dynamic transmitter reassignment.
Additionally, the resumption of emissions attributed with a high degree of confidence to the Firedrake system has been observed. This is the name used by the international radio monitoring community to refer to the Chinese-operated shortwave jamming system used to block broadcasts directed at audiences within Chinese territory. The name derives from a traditional Chinese melody that is continuously broadcast on the target frequency (instead of white noise) in order to mask the blocked station’s signal. In the EiBi database, it is listed under the designation CNR1 Jammer/Firedrake, as public sources attribute shared infrastructure with China National Radio 1 [2][3].
Finally, degradation of the GPS signal on the civil aviation route Incheon–Tokyo has been observed, as documented by the International Civil Aviation Organization (ICAO) [4]. This activity has been linked in various sources to GNSS interference capabilities attributed to the Pyongyang regime.
JAMMING AS AN INSTRUMENT OF INFORMATION CONTROL
The most significant action documented during the observation period is the systematic use of deliberate interference techniques (jamming) to block access to radio content considered hostile by various non-Western actors.
It has been observed that China carries out numerous operations in the radio frequency spectrum.
On the one hand, it has been observed that the 14.920 kHz AM frequency, assigned according to the EiBi database to the Taiwanese broadcaster Xi Wang Zhi Sheng (Sound of Hope), has been repeatedly overlaid by the CNR1 Jammer/Firedrake system. Technical analysis of the recordings confirms a 9–10 kHz bandwidth, continuous carrier, and a programmed and recurrent transmission pattern, all indicators of systematic rather than sporadic activity.
This practice is not limited to Taiwan. Systematic blocking through jamming techniques has also been observed against international information signals. One example is the blocking of the BBC World Service English service, rendering it unreceivable from Chinese territory.
However, this technique is not exclusively used by China. North Korea and Iran have also been observed employing similar signal suppression capabilities, adapted to their respective information control objectives.
In the case of the Democratic People’s Republic of Korea (DPRK), operations are focused against New Korea Hope Broadcasting on 7.200 MHz, an anti-communist North Korean broadcaster that Pyongyang systematically blocks using a high-power broadband jammer.
Additionally, jamming actions attributable to the Iranian regime have been observed targeting opposition services. These actions go beyond simple signal blocking, demonstrating adaptive jamming capability: when the broadcaster changes its transmission frequency, Iranian authorities reposition their jamming signal accordingly, shifting it from 15.750 MHz to 15.765 MHz in order to continue suppression. This real-time adaptation implies the existence of continuous adversary monitoring systems and rapid reassignment capability of high-power transmitters.
Figure 1 provides an aggregated geographic view of the events described.
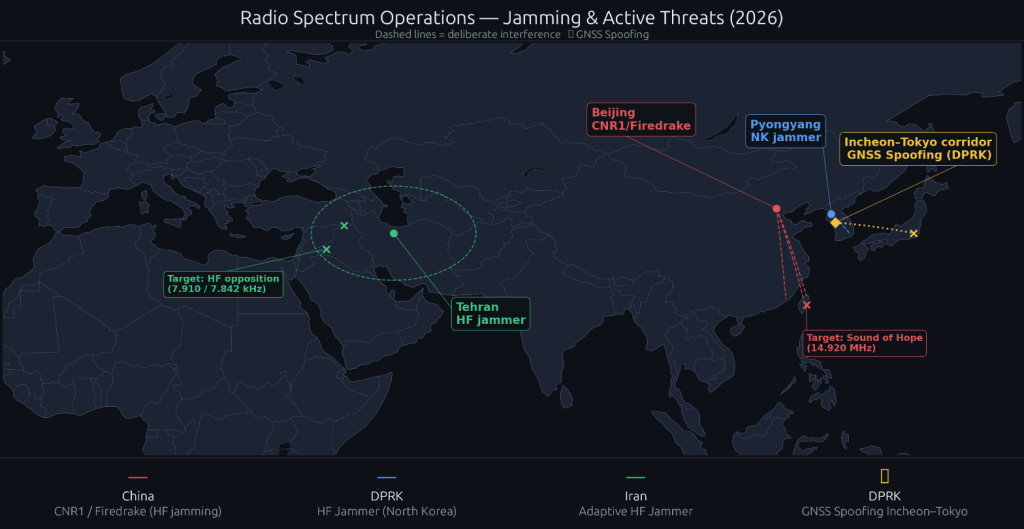
Figure 1 – Jamming and Active Threats (2026)
RADIO BROADCASTING AS AN INFLUENCE CAPABILITY
Radio transmissions are used by different states as a means of influence and message dissemination, functioning as instruments of narrative projection and public diplomacy.
China Radio International (CRI) operates a global high-power broadcast network, projecting toward Southeast Asia, the Middle East, Western Europe, and South America. It uses high-power and stable AM transmissions, which provide greater reception clarity and demonstrate sustained technological investment in this capability. Its global reach makes it one of the most geographically extensive public diplomacy instruments among non-Western actors.
Another example is PBS Xinjiang, which broadcasts in Uyghur and Mandarin on 3.950 and 4.500 MHz. This station operates in a region where China maintains documented policies of control and surveillance over the Uyghur population. The Office of the United Nations High Commissioner for Human Rights, in its August 2022 report, concluded that Chinese authorities have committed serious human rights violations in Xinjiang that may amount to international crimes, in particular crimes against humanity (OHCHR, “Xinjiang: UN Human Rights Office Assessment”, 31 August 2022) [5]. In this context, state broadcasting in Uyghur may constitute a narrative framing tool directed at a minority subject to mass surveillance and restrictions on freedoms.
Voice of Korea, the DPRK’s official external broadcaster, transmits in French, Korean, and Spanish on 12.015 MHz, projecting the Pyongyang regime’s discourse toward Western Europe and Latin America. Its multilingual output reflects a global outreach ambition that contrasts with the regime’s otherwise highly restrictive domestic information environment.
Finally, Iran has been observed projecting influence toward Turkey and Kurdistan through the Islamic Republic of Iran Broadcasting (IRIB), transmitting on medium wave (1.449–1.450 MHz) in Turkish with sufficient power to be received in the Eastern Mediterranean. This signal can reach Turkey, Azerbaijan, and the Turkic-speaking Central Asian republics, positioning Iranian broadcasting as an instrument of influence.
CONCLUSIONS
The evidence collected during the analyzed period supports the assessment, with a reasonable degree of certainty, that the use of the radio frequency spectrum by the actors under study does not reflect opportunistic behavior, but rather consolidated policies for the use of the electromagnetic domain as an instrument of foreign policy.
The existence of permanent infrastructure indicates sustained investment and long-term planning in capabilities that are not visible in conventional security debates.
In a context where competition between major powers increasingly takes place in grey-zone environments, the electromagnetic spectrum occupies a privileged position: it is simultaneously a battlefield, a medium of influence, and a command channel, which requires continuous monitoring.
[1] – European External Action Service (EEAS). Information Integrity and Countering Foreign Information Manipulation & Interference (FIMI). Disponible en: https://www.eeas.europa.eu/eeas/information-integrity-and-countering-foreign-information-manipulation-interference-fimi_en
[2] – EiBi. EiBi Shortwave Schedule and Frequency Database. Disponible en: http://www.eibispace.de
[3] – Radio Free Asia (RFA). Chinese Radio Jamming Monitoring and Frequency Information. Disponible en: https://www.rfa.org/english/about/frequencies.html
[4] – International Civil Aviation Organization (ICAO). GNSS Interference and Spoofing. Disponible en: https://www.icao.int/safety/FSIX/Pages/GNSS-Interference.aspx
[5] – Office of the United Nations High Commissioner for Human Rights (OHCHR). OHCHR Assessment of Human Rights Concerns in the Xinjiang Uyghur Autonomous Region, People’s Republic of China. 31 August 2022. Disponible en: https://www.ohchr.org/en/documents/country-reports/ohchr-assessment-human-rights-concerns-xinjiang-uyghur




Leave a Reply